🎬 Scene 1: Innocence Engineered

…But technology rarely stays pure. And every open door is an opportunity.
🎬 Scene 2: Weaponized Code
What began as a support tool evolved into one of the most invasive spyware tools the world had seen — Pegasus.
🎬 Scene 3: The Clickless Intruder
No links. No downloads. Just a silent message. And now the phone belongs to someone else.
🎬 Scene 4: The Listener Awakens
Pegasus activates silently. Listens, watches, records — without ever revealing itself.
🎬 Scene 5: Eyes in the Wrong Places
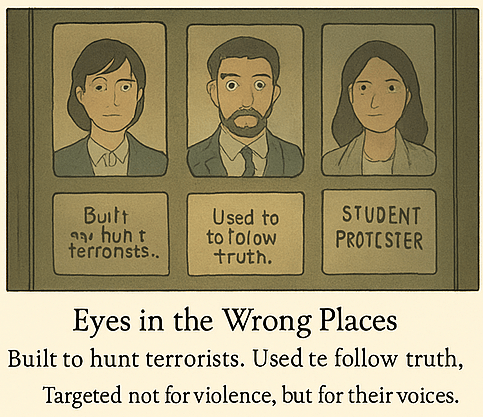
It was marketed as a counter-terrorism tool. But the real targets told another story.
🎬 Scene 6: The Ghost in the Phone
Once infected, Pegasus is almost impossible to detect. And harder to trace.
🎬 Scene 7: Silent But Global
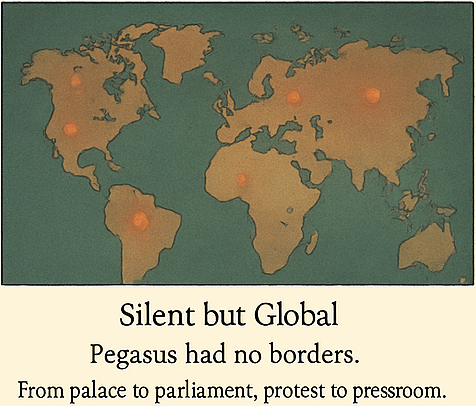
Mexico, India, Saudi Arabia, Hungary…
“Dozens of governments. Thousands of devices. No battlefield needed.”
🎬 Scene 8: Denial and Disclosure
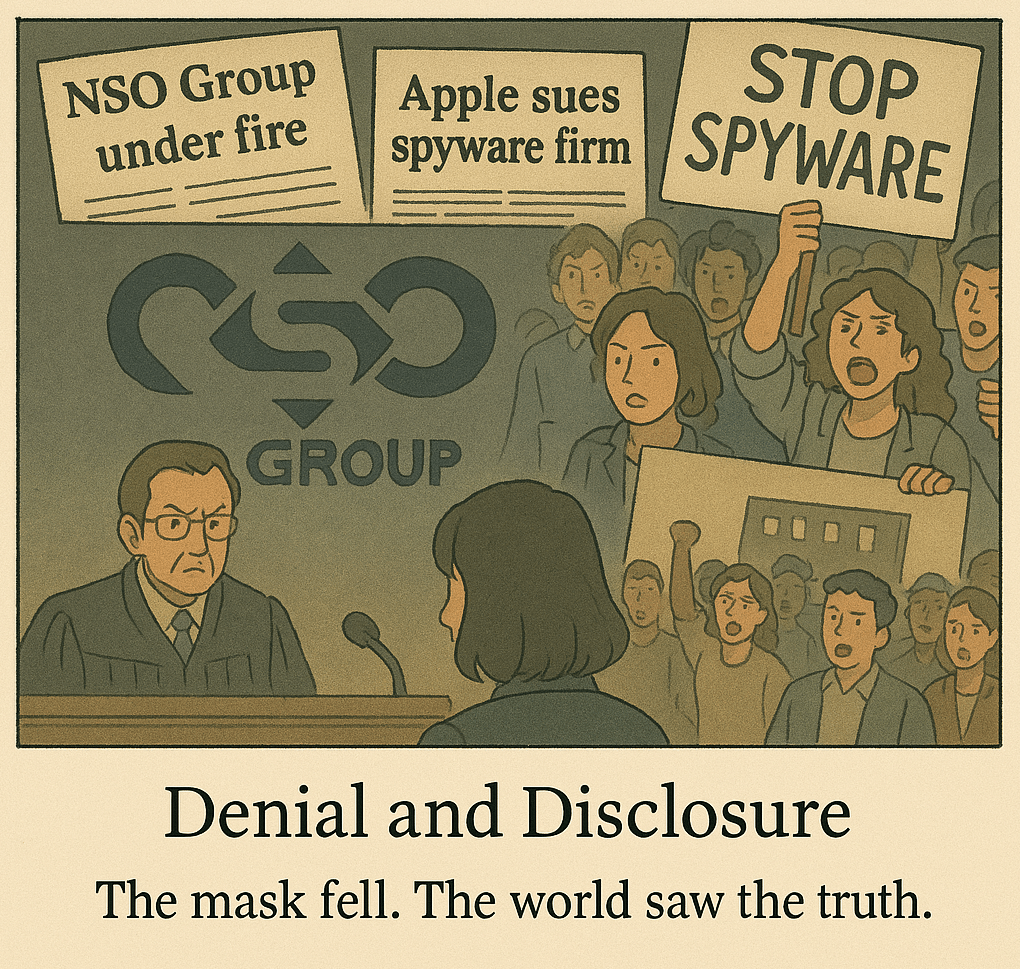
The world took notice. Lawsuits. Outrage. Investigations.
🎬 Scene 9: The Self-Destructing Shadow
Pegasus leaves no trace. It vanishes when its job is done.
🎬 Scene 10: Your Phone Isn’t Just Yours
The most dangerous spyware doesn’t need to be installed. It just needs to be invited — silently.
📎 Epilogue: How Pegasus Changed the Game
👾 Developer: NSO Group, Israel
🎯 Claimed Use: Anti-terrorism surveillance
🧪 Reality: Used against journalists, lawyers, activists, and opposition leaders
🔓 Entry Method: Zero-click exploits via iMessage and WhatsApp
💥 Detection: Nearly impossible; often self-destructs
⚖️ Fallout: Apple sued NSO Group. Global outcry. Pegasus Project revealed abuse at scale.
“The line between support tool and surveillance weapon is thinner than we think.”