Backdoor in the Brightest Star
🎬 Scene 1: The Trusted Star
“Used by the best. Trusted by all. A shining star in IT management.”
🎬 Scene 2: In the Shadows of Orion
SUNBURST, a trojanized update. Signed, sealed, delivered
🎬 Scene 3: Silent Delivery
Just another update. No one suspected the constellation was burning.
🎬 Scene 4: Sleeping Payload
It waited. For days. For weeks. For instructions.
🎬 Scene 5: The Backdoor Opens
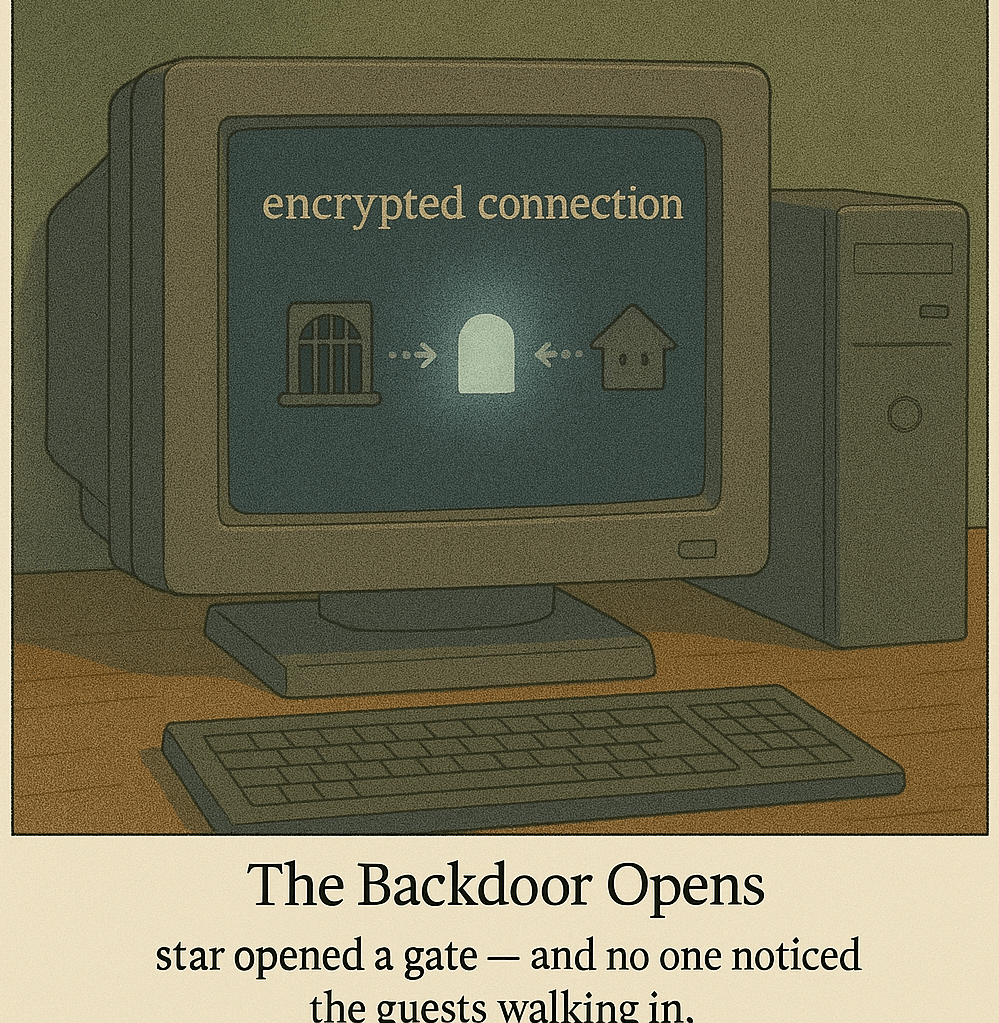
The star opened a gate — and no one noticed the guests walking in.
🎬 Scene 6: Into the Crown Jewels
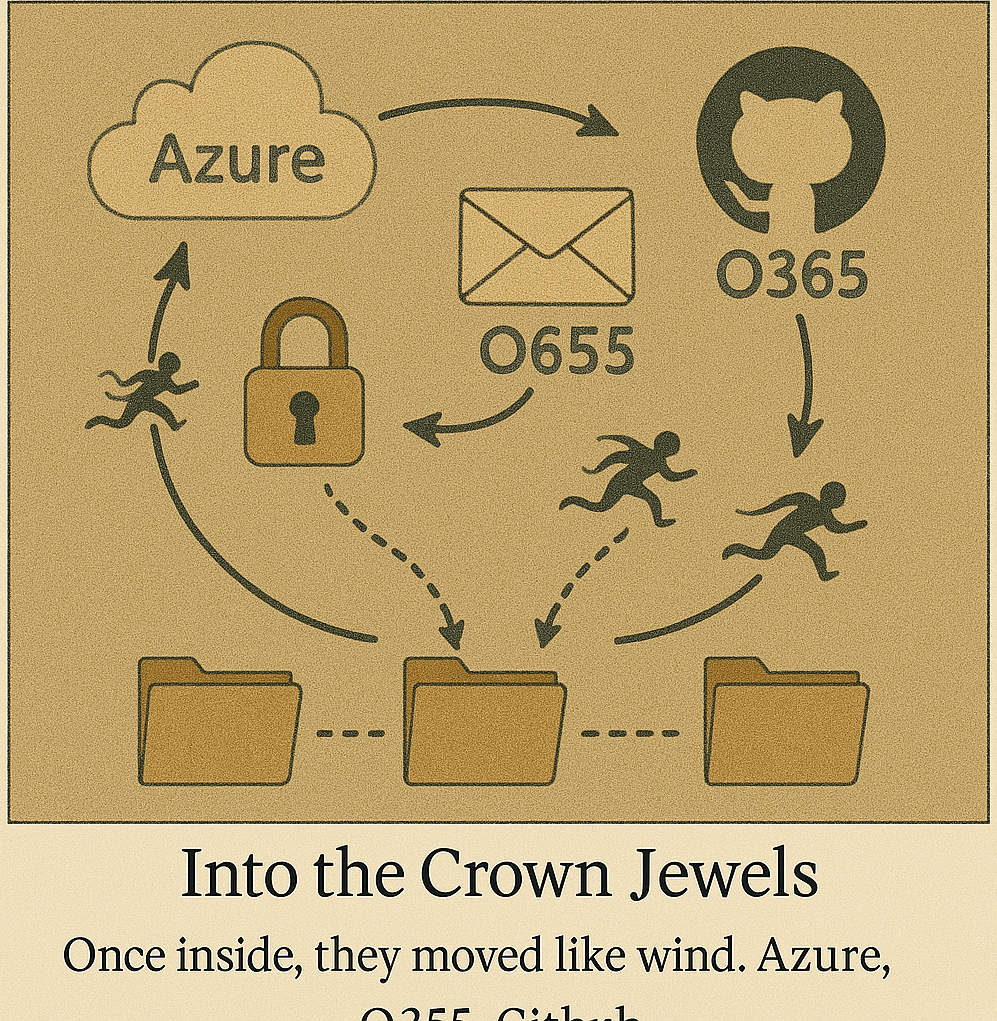
Once inside, they moved like wind. Azure, O365, GitHub, SAML.
🎬 Scene 7: Victims Across the Globe
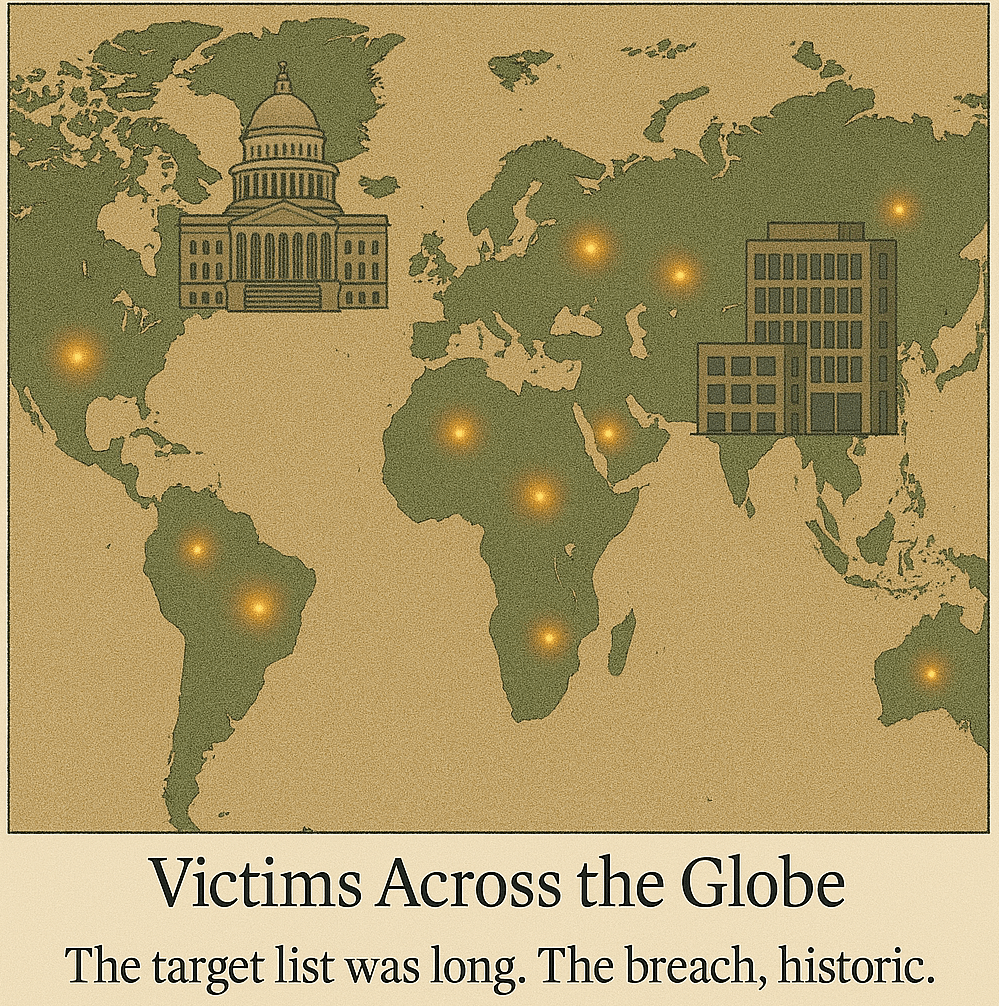
The target list was long. The breach, historic.
🎬 Scene 8: The Unmasking
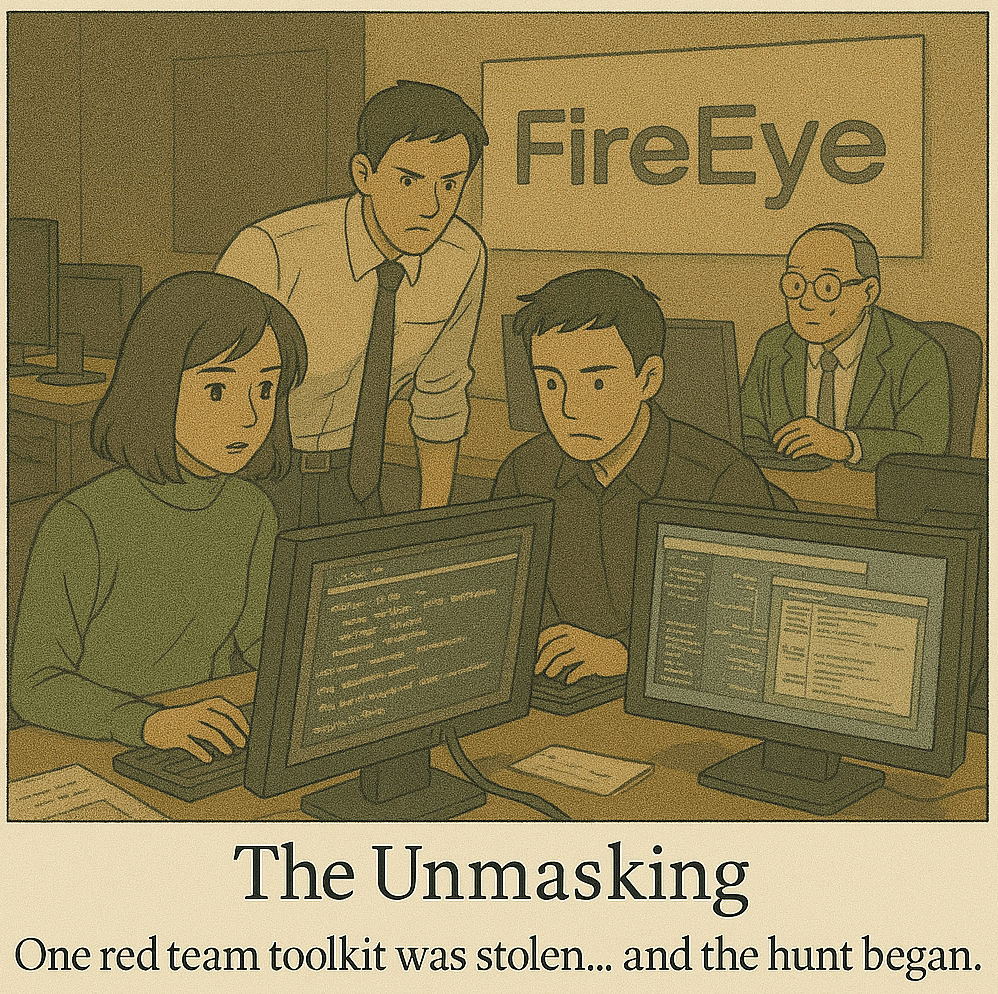
“One red team toolkit was stolen… and the hunt began.”
🎬 Scene 9: Echoes in the Cloud
“The breach didn’t end with the patch. It echoed across identity and trust.”
🎬 Scene 10: A Lesson in Light
“Even the brightest stars cast shadows. Trust must be earned — again.”
🧩 Resolution of the SolarWinds Incident
🔍 Discovery & Initial Response
- FireEye was the first to discover the compromise in December 2020, during an internal investigation into their red team toolkit theft.
- They identified SUNBURST, a backdoor planted in SolarWinds’ Orion software updates, which had been shipped to ~18,000 customers.
🧨 Scope & Impact
- The breach allowed attackers to impersonate users and federated domains via SAML token forgery.
- High-profile victims included:
- US Treasury, State, Commerce, Homeland Security
- Microsoft, Cisco, Intel
- Think tanks, private companies, and universities
🛡️ Mitigation & Government Response
- Emergency Directive 21-01 issued by CISA: all federal agencies were ordered to disconnect SolarWinds Orion.
- CISA, NSA, FBI, and ODNI formed a Unified Coordination Group.
- Microsoft, FireEye, and CrowdStrike released detections and countermeasures.
- SolarWinds released patches and rebuilt the Orion software pipeline.
⚖️ Accountability
- In 2023, the SEC filed charges against SolarWinds’ CISO for allegedly misleading investors and failing to disclose known risks.
- It became a watershed moment in cybersecurity liability and executive accountability.
📜 Policy Aftermath
Increased emphasis on supply chain security and code signing practices
- Resulted in Executive Order 14028 on Improving the Nation’s Cybersecurity:
- Push for Zero Trust architecture
- Mandate for Software Bill of Materials (SBOM)
📎 Epilogue: The Fallout from SolarWinds
🧨 Attack Vector: Trojanized Orion updates (SUNBURST malware)
🎯 Targeted: U.S. government agencies, Microsoft, security firms, global enterprises
🔓 Techniques: Supply chain compromise, SAML forgery, privilege escalation
🧾 Resolution: Orion software rebuilt, patches deployed, Executive Order issued
⚖️ Accountability: SEC lawsuit against SolarWinds CISO (2023), redefined corporate cyber risk
🔐 Legacy: Accelerated adoption of Zero Trust, SBOM, and secure software pipelines
“The real breach wasn’t just in code — it was in trust.”