How a Line of Code Shook a Nuclear Nation….
It didn’t crawl in through a dropped USB, as the tale was told.
It was already there.
Hidden inside a controller —
Disguised as a pump. Installed with purpose. Waiting.

Inside the Natanz uranium enrichment plant, machines spun at 1,064 revolutions per minute.
The worm waited, learning their rhythm… then changed the song.
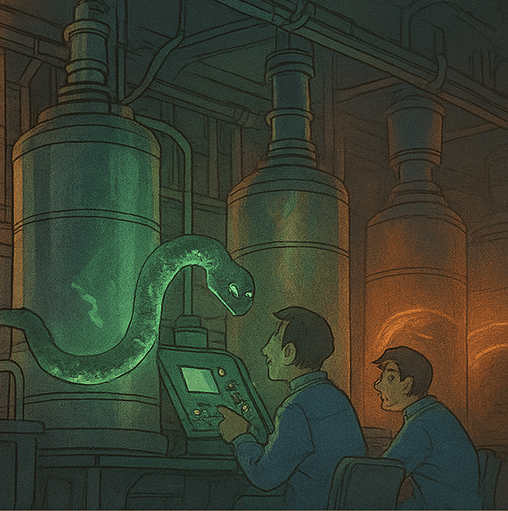
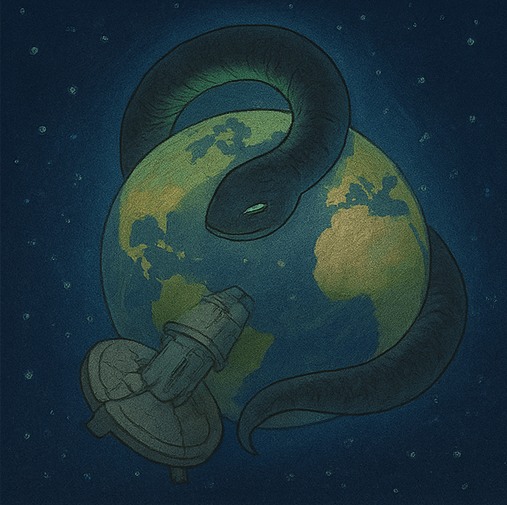
A worm slithering through a glowing PLC (programmable logic controller)
It sped them up.
Slowed them down.
Damaged rotors, caused cracks — and lied to the engineers the entire time.
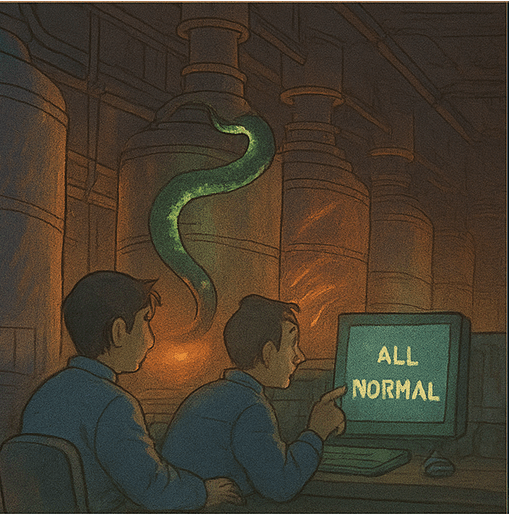
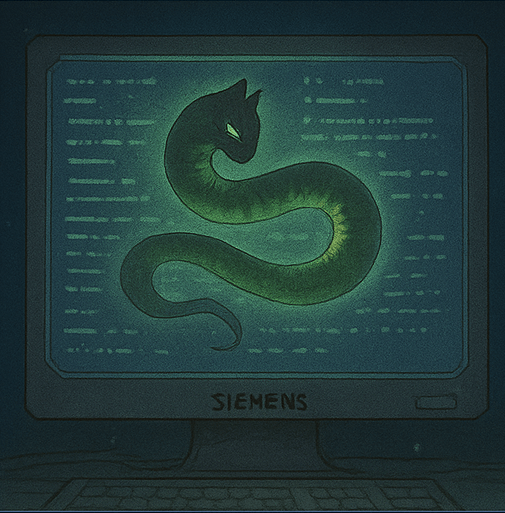
It knew the brand: Siemens.
It rewrote PLC logic, mimicking trusted operations.
It was invisible — a ghost in firmware.
It was found not by spies, but by accident.
A Belarusian antivirus team found the worm outside its nest.
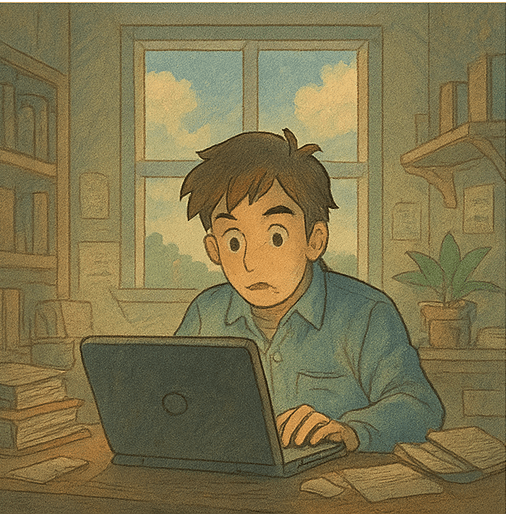
Reverse engineers from VirusBlokAda staring at unknown binary blobs
Stuxnet was the first worm to jump from code to geopolitics.
A cyberweapon designed to delay a nuclear program — without firing a missile.
It changed everything.
From Stuxnet came Flame, Duqu, and a new cyber era —
where code doesn’t just crash computers… it can start wars.
References:
https://spectrum.ieee.org/the-real-story-of-stuxnet
https://en.wikipedia.org/wiki/Stuxnet
https://www.sciencedirect.com/topics/computer-science/stuxnet